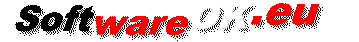
How to check whether your PC has a Trusted Platform Module (TPM) for more security on your Windows 11, 10, ... etc. PC!If you are planning to upgrade from Windows 10 to Windows 11 or are using encryption features, you need to make sure that the device has a TPM chip. Here are a few ways to find out without reading a manual. Check in the PC Bios whether this has possibly not been activated! 1.) ... Detect with the command tpm.msc whether it was recognized on the PC!
|
| (Image-1) How do I know if I have TPM on Windows! |
 |
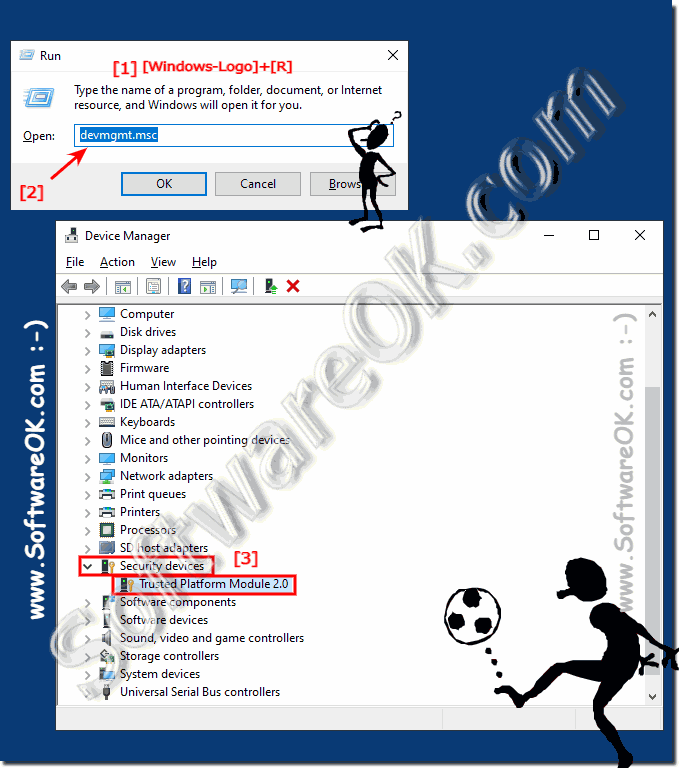
2.) Detect in the Windows device manager whether TPM is present!
1. Start the Windows Device Manager as always2. And see whether the Trusted Platform Module is present
(... see Image-2 Point 1 to 3)
| (Image-2) Find TPM on Windows 11, 10, ... Device Manager! |
 |
3.) What is the Trusted Platform Module (TPM) good for?
TPM (Trusted Platform Module) is a computer chip, or rather a microcontroller, which can securely store artifacts that are used to authenticate the platform of your PC, laptop, .... These artifacts can be passwords, certificates, or encryption keys.
The TPM contains a unique cryptographic key and can therefore be used to identify the computer and can help ensure that the platform remains trustworthy.
For example, to ensure with PC authentication that the platform is what it claims to be!
Further information:
► https://trustedcomputinggroup.org/resource/trusted-platform-module-tpm-summary/
The TPM contains a unique cryptographic key and can therefore be used to identify the computer and can help ensure that the platform remains trustworthy.
For example, to ensure with PC authentication that the platform is what it claims to be!
Further information:
► https://trustedcomputinggroup.org/resource/trusted-platform-module-tpm-summary/
The Trusted Platform Module (TPM) is a hardware security chip found on many modern computers and other devices. It serves to increase the security and integrity of the system by providing various functions:
1. Secure Boot:
TPM enables Secure Boot, ensuring only trusted software and firmware are loaded during boot. This reduces the risk of malware attacks.
2. Encryption:
TPM can be used to encrypt data. For example, it can generate and store keys used to decrypt hard drives or authenticate users.
3. Integrity Measurements:
TPM can monitor the integrity of the system by taking measurements of system components such as bootloader, operating system and drivers. These measurements can be used to ensure that the system has not been compromised.
4. Secure Key Storage:
TPM provides a secure storage space for cryptographic keys. These keys can be used to protect sensitive data or to verify the identity of the system.
Overall, the TPM helps improve the security and trustworthiness of computers and other electronic devices by providing a range of security features that help protect the integrity of the system and ensure the confidentiality of data.
FAQ 161: Updated on: 28 April 2024 11:27